What Are Zero-Knowledge Proofs? A Simple Explanation of ZK Proofs
Zero-knowledge proofs let you prove something is true without showing the data behind it. They're the cryptographic backbone of privacy coins, zk-rollups, and on-chain identity systems. First theorised in 1985, ZK proofs are now production infrastructure across DeFi, scaling, and compliance. |
Every transaction on a public blockchain is exactly that. Public. Your wallet balance, your transaction history, every move you make, all sitting on a ledger that anyone with an internet connection can read.
That transparency is the whole point of a blockchain. It's also the problem.
Because verification has always meant disclosure. You prove you have the funds by showing the funds. You prove your identity by handing over your documents. You prove compliance by opening the books. The person checking gets to see everything.
Zero-knowledge proofs break that tradeoff. They let you prove a claim is valid, mathematically, cryptographically, with near-certainty, without revealing a single piece of the underlying data. The verifier learns one thing: the statement is true. That's it.
The technology started as a theoretical concept in an academic paper that got rejected three times. Four decades later, it's running production infrastructure across Ethereum Layer 2 networks, privacy-focused blockchains, and digital identity systems used by entire countries.
Here's how it all works.
What You'll Learn About ZK Proofs
→ What a zero-knowledge proof is and where the concept came from
→ How zero-knowledge proofs work at a practical level, plus a deeper technical breakdown you can skip
→ The three properties every ZK proof has to satisfy
→ Interactive vs non-interactive proofs and why blockchains need the second kind
→ SNARKs, STARKs, and Bulletproofs, and what separates them
→ Where ZK proofs show up in crypto right now, from privacy to identity
What Is a Zero-Knowledge Proof?
A zero-knowledge proof is a cryptographic method where one party (the prover) convinces another party (the verifier) that a specific statement is true. The verifier learns absolutely nothing beyond the fact that the statement is true. Not the data. Not the method. Nothing.
Three researchers at MIT made this idea formal in 1985. Shafi Goldwasser, Silvio Micali, and Charles Rackoff published a paper called "The Knowledge Complexity of Interactive Proof Systems." It got rejected three times before anyone would publish it. Goldwasser and Micali later won the 2012 Turing Award partly for that work.
The concept sat in academic papers for decades. Then crypto showed up and gave it a reason to exist.
How Does Zero-Knowledge Proof Work?
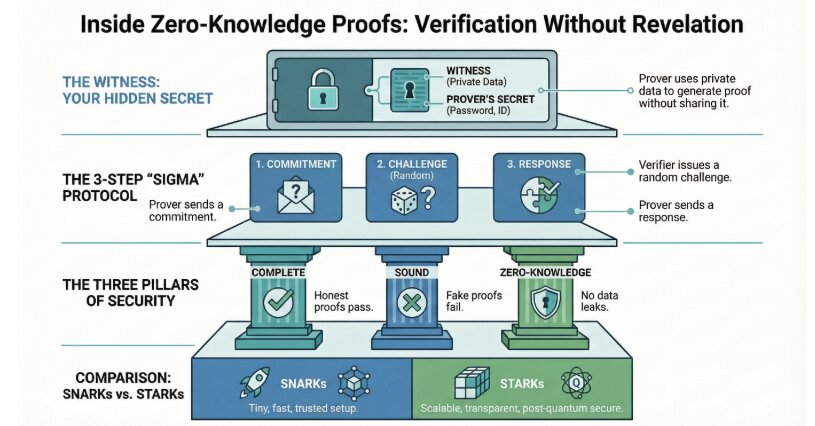
Two roles. A prover and a verifier. The prover holds some private data and wants to convince the verifier that a claim about that data is true. The verifier needs to be convinced without ever seeing the data itself.
In crypto terms, you want to prove you have enough funds to cover a transaction. You're the prover. The blockchain network is the verifier. Instead of exposing your wallet balance to the entire network, you generate a ZK proof. The network checks it. If it's valid, the transaction goes through. Your balance stays private.
The proof itself is just a small piece of cryptographic output. It doesn't contain your data. It doesn't encrypt your data. It mathematically confirms that your claim checks out. That's an important distinction. Encryption hides data and lets authorised parties decrypt it later. ZK proofs validate truth claims. The data was never shared in the first place.
The Three Properties of ZK Proofs
Every legitimate zero-knowledge proof satisfies three conditions. All three. No exceptions.
Completeness. If the statement is true, the proof will always convince an honest verifier. No false rejections. You have the funds? The proof confirms it. Every time.
Soundness. If the statement is false, no amount of clever manipulation will produce a valid proof. You don't have the funds? You can't fake your way through. The probability of a successful bluff is mathematically negligible.
Zero-knowledge. The verifier learns nothing except that the statement is true. Not the underlying data. Not a hint about it. Not even metadata that could help narrow it down. The proof gives up exactly one bit of information: valid or not valid.
Interactive vs Non-Interactive ZK Proofs
The original 1985 design required the prover and verifier to go back and forth. Multiple rounds. Questions and responses. The verifier would challenge the prover repeatedly, and each successful response increased confidence that the proof was legitimate.
That's fine for a conversation between two people. It's useless for a blockchain.
A blockchain doesn't have back-and-forth conversations. A transaction gets submitted, validated, and either accepted or rejected. No one's sitting there asking follow-up questions.
Non-interactive zero-knowledge proofs solved this. The prover generates a single proof. Anyone can verify it. No interaction required. The proof sits there on-chain, valid for anyone who checks it, forever.
This is the version crypto uses. Every ZK application you've heard of runs on non-interactive proofs.
ZK Proofs Under the Hood
You've got enough to understand what ZK proofs do. Feel free to skip ahead to the types of ZK proofs. But if you're curious about what's happening at the cryptographic level, here's the breakdown.
Three components make up every ZK proof system:
Component | What It Is | Who Sees It |
Witness | The secret input (your private data) | Prover only |
Public Input | The claim being proved (e.g., "this transaction is valid") | Both parties |
Circuit | The mathematical rules that define what counts as a valid proof | Both parties |
What the prover does: Takes the witness and the public input, runs them through the circuit, and produces a proof. That proof is a set of cryptographic commitments. Think of commitments as sealed envelopes. The prover locks values inside them. The values can be verified against the circuit's constraints without ever being opened.
What the verifier does: Takes the proof and the public input, runs checks against the circuit's structure, and confirms whether the commitments are consistent. Everything lines up? Valid. Any commitment contradicts the circuit? Fails.
Where the cryptography differs:
SNARKs use polynomial equations over elliptic curves
STARKs use hash-based polynomial commitments
The details differ. The principle is the same: the prover demonstrates knowledge of a valid witness without revealing it, and the verifier confirms this through algebraic checks that would be computationally impossible to fake.
Types of ZK Proofs Used in Crypto
Three main flavours show up across crypto projects. They all do the same thing but make different tradeoffs.
zk-SNARKs
Zero-Knowledge Succinct Non-Interactive Argument of Knowledge. The name is a mouthful. The proofs are tiny. That's the point.
SNARKs produce very small proofs that verify fast. A few hundred bytes can prove the validity of thousands of transactions. Zcash was the first cryptocurrency to deploy them in production back in 2016. Mina Protocol took it further, using recursive SNARKs to compress its entire blockchain to roughly 22KB. The whole chain. On your phone.
But traditional SNARKs require a "trusted setup." That's a one-time ceremony where initial parameters get generated. If the people running that ceremony kept the underlying data, they could theoretically forge proofs. Newer implementations have reduced this risk, but it's still a valid criticism.
SNARKs also rely on elliptic curve cryptography. That makes them potentially vulnerable to quantum computing. Not today. But eventually.
zk-STARKs
Zero-Knowledge Scalable Transparent Argument of Knowledge. Developed by Eli Ben-Sasson and his team at StarkWare.
STARKs skip the trusted setup entirely. Transparent from the start. They use hash functions instead of elliptic curves, which makes them resistant to quantum attacks. They also scale better for large computations.
They're bigger though. STARK proofs take up more space than SNARK proofs, which means more data on-chain and higher verification costs. Starknet, one of Ethereum's major Layer 2 networks, runs on STARKs.
Bulletproofs
Less well-known, but they show up in some important places. Bulletproofs don't need a trusted setup and produce reasonably compact proofs. They're slower to verify than SNARKs but work well in specific contexts. Monero uses a version of Bulletproofs to hide transaction amounts without bloating the chain.
Feature | zk-SNARKs | zk-STARKs | Bulletproofs |
Proof Size | Very small | Larger | Medium |
Trusted Setup | Yes (traditionally) | No | No |
Quantum Resistant | No | Yes | No |
Verification Speed | Fast | Moderate | Slower |
Used By | Zcash, Mina | Starknet | Monero |
Where ZK Proofs Show Up in Crypto
The technology has moved way past academic papers and single-use privacy coins. Here's where it's actually running right now.
Scaling with zk-rollups. ZK-rollups bundle thousands of transactions off-chain, then submit a single validity proof to Ethereum's mainnet. Massively lower gas fees. Higher throughput. No sacrifice on security. zkSync and Starknet are the two biggest players here, and both are processing real transactions at scale.
Privacy coins. Zcash built its entire privacy model on zk-SNARKs. Shielded transactions prove validity without revealing sender, receiver, or amount. Iron Fish took a similar approach with mandatory privacy on every transaction. Privacy coins were the original crypto use case for ZK proofs, and they're still surviving despite regulatory hurdles.
Identity verification. Proving you're a real human, over 18, not on a sanctions list, or a resident of a specific country. All without handing over your passport or driver's license. Worldcoin uses ZK proofs through the Semaphore protocol to verify unique personhood. Bhutan built a national digital identity system on Ethereum using the same principle.
Private smart contracts. Aztec Network is building a privacy-first Layer 2 where smart contract inputs and outputs stay encrypted. Developers can build DeFi applications where your position sizes, strategies, and balances don't sit on a public ledger for the world to see.
Compliant privacy. This is the big trend heading into 2026 and beyond. ZK proofs let you prove regulatory compliance without exposing private data. Pass a KYC check without revealing your address. Confirm crypto tax reporting without opening your full transaction history. Aleph Zero is building its entire model around this concept. It's probably the only version of on-chain privacy that survives long-term in regulated markets.
What’s Next?
ZK proofs started as a theoretical curiosity in 1985. Forty years later, they're running production infrastructure that handles billions in transaction volume.
The trajectory is clear. Scaling solutions need them. Privacy needs them. Regulatory compliance needs them. The projects built with ZK technology aren't fringe experiments anymore. They're the infrastructure layer on which the next generation of crypto runs.
Go Further With Learning Crypto
ZK proofs are changing how transactions get validated, how privacy works on-chain, and which projects are worth paying attention to.
Learning Crypto's Ask Crypto AI copilot pulls live, verifiable on-chain data so you can see what's actually happening instead of trusting someone else's summary.
Track smart-money flows, spot red flags in tokenomics, and do your own research with real numbers.
FAQs
Are zero-knowledge proofs anonymous?
Not by themselves. ZK proofs validate that a statement is true without revealing the data behind it. That's verification, not anonymity. A well-designed protocol can use ZK proofs to achieve strong privacy guarantees. But the proof alone doesn't make you anonymous.
Are ZK proofs only used in crypto?
No. Healthcare systems use them to verify patient eligibility without exposing medical records. Financial institutions use them for KYC compliance without sharing customer data across organisations. AI developers are exploring ZK proofs to verify that a model was trained on a specific dataset without revealing the training data.
Crypto is the most visible use case, but the technology applies anywhere you need to prove something without showing it.
Do ZK proofs replace encryption?
No. They solve different problems. Encryption hides data so only authorised parties can read it. ZK proofs prove a claim is true without sharing the data at all. They're complementary. Some systems use both, but one doesn't replace the other.
Can zero-knowledge proofs be hacked or faked?
Not in any practical sense. The soundness property means a false statement can't produce a valid proof. The probability of faking one is so small it's effectively zero. That said, the implementation around the proof can have vulnerabilities. A buggy smart contract, a compromised trusted setup, or a poorly written circuit could all create weaknesses. The math is solid. The code built on top of it is where things can go wrong.
Will quantum computers break zero-knowledge proofs?
Depends on the type. SNARKs rely on elliptic curve cryptography, which quantum computers could, in theory, break. STARKs use hash functions, which are considered quantum-resistant. The quantum threat isn't immediate, but it's a real concern that newer projects are building with post-quantum security in mind. If you're evaluating ZK projects long-term, it's worth checking which proof system they use.
Disclaimer: This article is for educational purposes only and does not constitute financial advice. Cryptocurrency investments carry risk; you should always do your own research before making any investment decisions.
Heidi Chakos is co-founder of LearningCrypto and creator of the @cryptotips YouTube channel. A cryptocurrency educator and author with over a decade in the space, she specialises in Bitcoin fundamentals, self-custody, and on-chain analytics. Follow her on X at @blockchainchick.
View all articles →